Hardware components
Delivery and installation of HSM modules
Sale, delivery, lease and installation of Thales and Entrust HSM servers




Secure storage of cryptographic data and digital keys
HSM modules (Hardware Security Module) are a hardware part of the PKI infrastructure. They ensure the protection of all sensitive company data, especially certification authorities, cryptographic keys or system SSL cretificates. We install and sell these modules.

HSM server as an anchor of trust within the organization
The central point of trust is the foundation of an organization’s cryptographic system. Digital security relies on cryptographic keys to encrypt and decrypt data and perform functions such as signing signatures, verifying signatures, and other cryptographic operations. These keys must be protected in special devices.
That is why we use HSM modules from Thales (formerly Gemalto) and Entrust in our projects. We can not only deliver and configure these devices, but also connect them to your organization’s ecosystem and PKI infrastructure.
In addition to the installation itself, we will also mediate their direct sale.

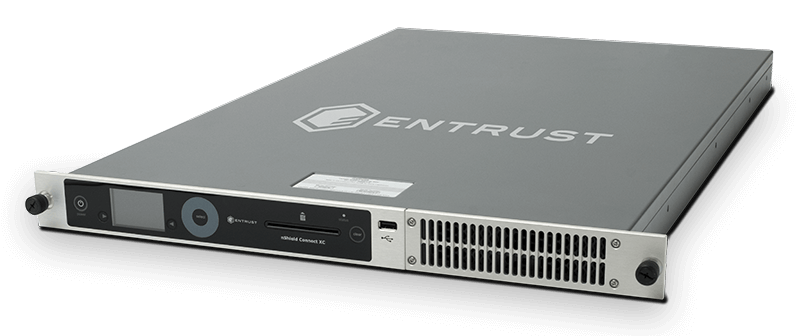
Entrust HSM modules (nShield HSMs)
Entrust delivers comprehensive and advanced data security solutions that enable customers to create strong protection across devices, processes, platforms, and environments. nShield HSMs are tamper-proof devices that protect customers’ most sensitive data.
They provide a secure environment for generating strong cryptographic keys and performing cryptographic operations, including encryption, decryption, signing, and authentication. With nShield HSMs, they never leave the physical HSM in an unprotected form.

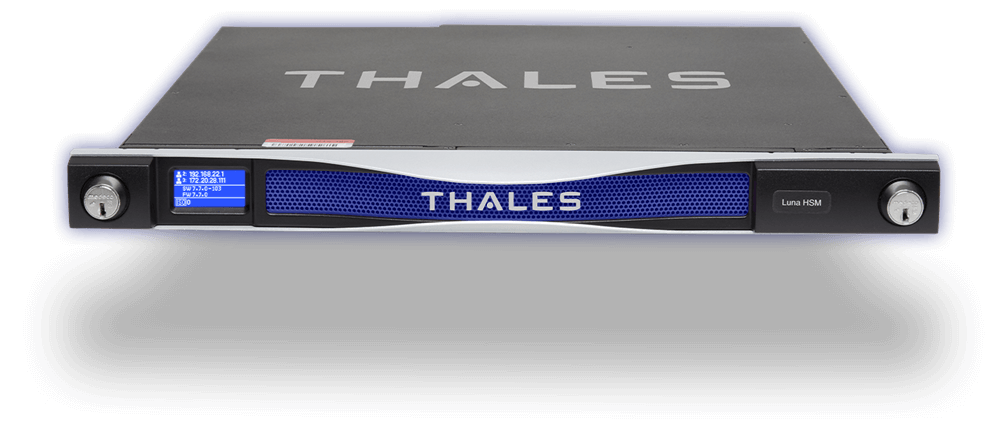
Thales HSM modules (formerly Gemalto)
Highly secure, tamper-proof, high-end devices offering top performance. Protects the entire cryptographic key lifecycle within the verified constraints of Thales Luna Network HSMs. This approach places Thales products among the most trusted general purpose HSMs on the market.
Unlike other key storage methods that move keys outside of HSMs to the “trusted tier”, in Thales modules cryptographic data is always under both physical and logical protection.
We either install these devices as part of our solutions or sell them as separate products. Contact us to get a specific offer.
Are you interested in our solution? Contact us
